RFIDtect
Detektiert RFID Lesegeräte und wertet die Trägerfrequenz aus
Immer häufiger findet man Kontaktlose ("RFID") Chipkarten - ob als Zutrittssystem oder Bezahlkarte. Wer sich nun etwas genauer mit solchen Sytemen befasst wird feststellen das in der Industrie zwei relativ weit verbreitete Standartds üblich sind. Zum einen werden für einfache Türöffner unsichere 125KHz Read-Only Transponder verwendet; das sich diese mithilfe eines iPod und einigen wenigen Bauteilen Clonen lassen hat der Chaos Computer Club bereits gezeigt. Das zweite verbreitete System basiert auf der 13,56MHz Mifare Transpondertechnik von Philips NXP. Dieses verfügt über eine verschlüsselte Übertragung und ein Rechtemanagement einzelner Sektoren auf der Chipkarte - ist also gewissermaßen eine Nummer intelligenter.
Möchte man sich nun mit dem Reverse Engineering eines solchen Chipkartensystems befassen, muss man selbstverständlich zuerst wissen mit welchem System man zu tun hat. Wenn man im Besitz einer Chipkarte ist könnte man verschiedene Lesegeräte ausprobieren, hat man keine muss man über das Lesegerät Rückschlüsse aufs System ziehen.
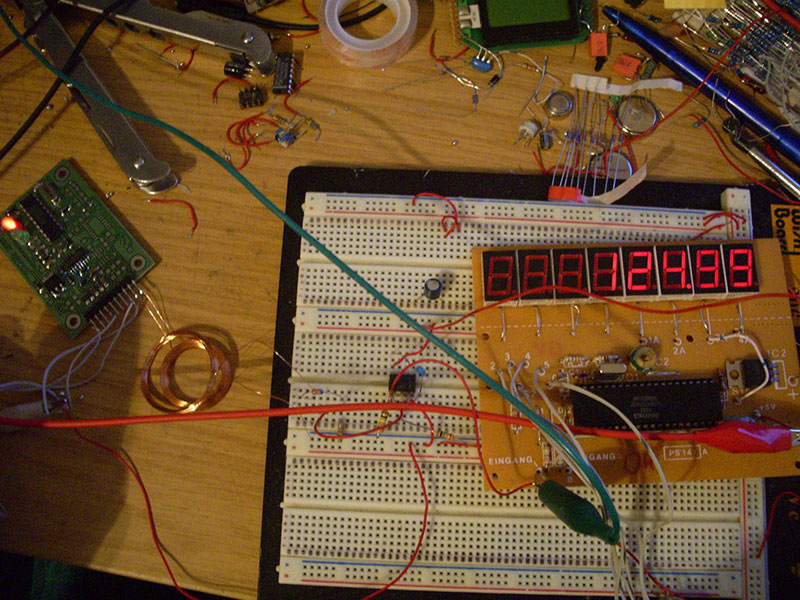
Die Transponder - ob nun in Form einer ISO Chipkarte, eines Schlüsselanhängers oder einer winzigen Glaskapsel - werden über das Lesegerät mit Strom versorgt. Dieses geschieht über ein magnetisches Feld welches mit einer bestimmten Trägerfrequenz vom Leser abgestrahlt wird.
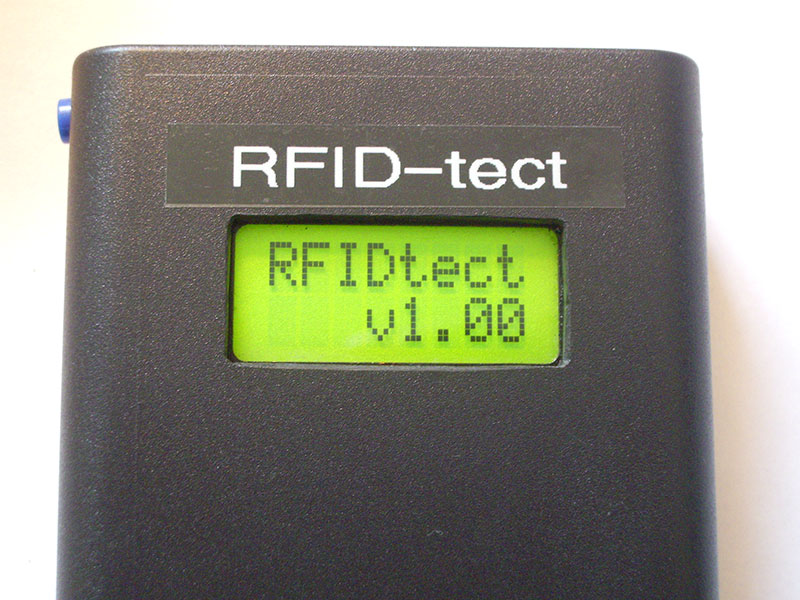
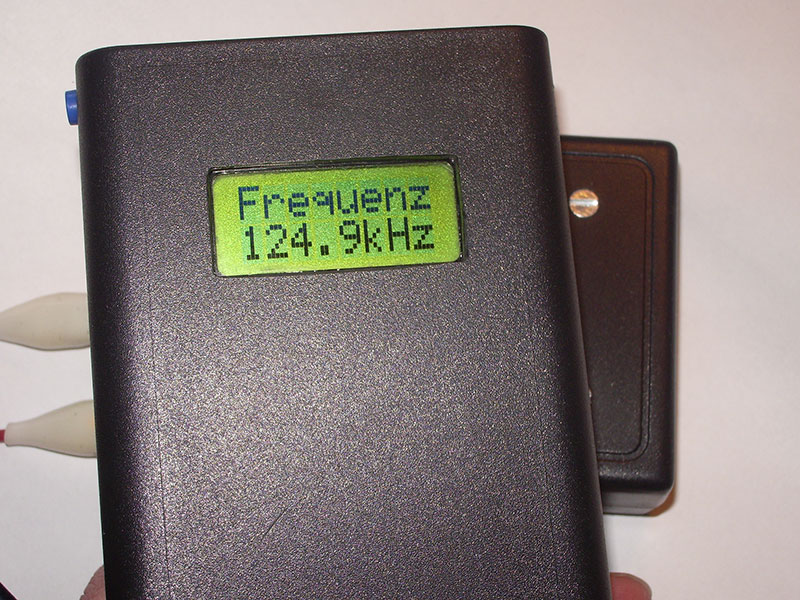
Verbindet man eine Drahtspule mit einem empfindlichen Frequenzzähler und führt sie in das Feld des Lesegerätes so zeigt dieser die Trägerfrequenz an.
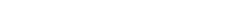
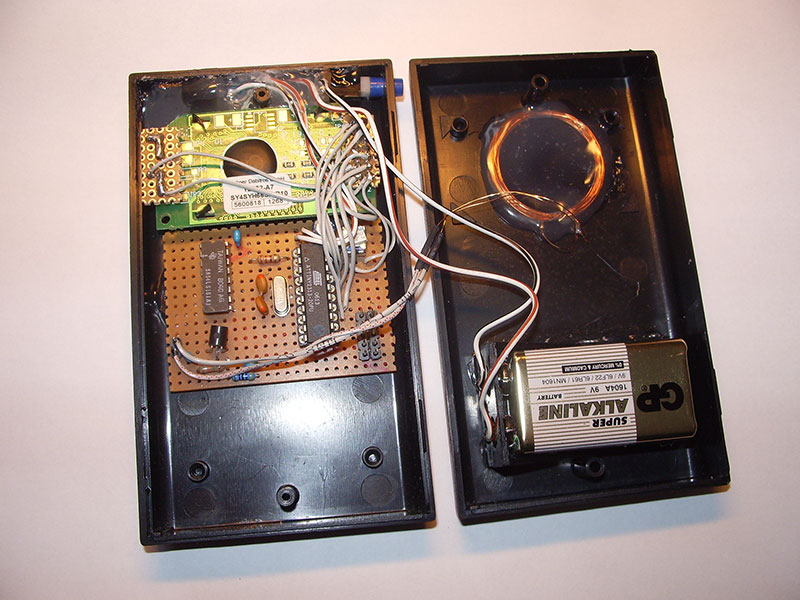
Genau diese Aufgabe hat RFIDtect: Das von der im Gerät verbauten Spule empfangene Trägersignal wird verstärkt, heruntergeteilt und von einem Atmel Mikrocontroller ausgewertet. Das LC Display zeigt die erkannte Trägerfrequenz an.
Man kann mit diesem Gerät KEINE versteckten RFID Transponderchips aufspüren. Den nötigen Träger senden nur die passenden Lesegeräte aus.
Zu diesem Projekt existieren leider keine Schaltpläne oder Unterlagen mehr. Es soll daher lediglich als Denkanstoß für eigene Entwicklungen gelten.